CS205 Assignment 1 Solution and Discussion
-
Assignment No. 01
Semester: Fall 2019
CS205: Information Security Total Marks: 15

Due Date: 14/11/2019
Instructions:
Please read the following instructions carefully before submitting assignment:
You need to use MS word document to prepare and submit the assignment on VU-LMS.
It should be clear that your assignment will not get any credit if:- The assignment is submitted after due date.
- The assignment is not in the required format (doc or docx)
- The submitted assignment does not open or file is corrupt.
- Assignment is copied (partial or full) from any source (websites, forums, students, etc)
Objectives:
To enhance the learning capabilities of the students about:
• Security model
• OSI security architectureAssignment
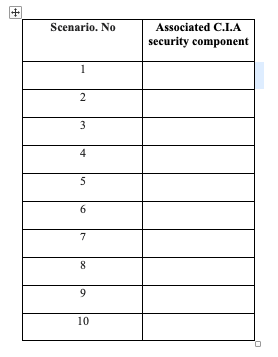
Question No.1:
Carefully study the scenarios given below with respect to C.I.A triangle and identify the C.I.A. security component associated with each scenario. You are required to provide your answer in table given below:
- Student’s grade information is considered very important and it should be available only for that specific student rather than other students.
- Information of heart patient is stored in hospital’s database. The doctor trusts on that stored information and then suggests medicine according to this information. Another employee who has also legal rights to access this database, unintentionally changes this information that can misguide the patient treatment.
- VU-LMS is not accessible due to which students are not able to submit their assignments on time.
- An ATM machine is not responding due to general processing error.
- Employee’s salary slip in an organization should not be visible to any other employee.
- Product price and specification available on online shopping store is changed by unauthorized person.
- You are replying to an email of your friend then it should be received in original form as it is sent by you.
- Your academic marks are posted on social media website by some unauthorized person.
- A student is checking his/her result online but website is not responding.
- A multinational company makes a plan for launching a new product for capturing customers in a market but this plan leaked to its competitor.
Solution:
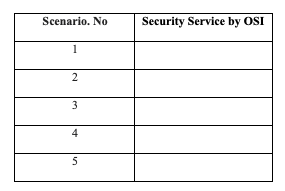
Question No.2:
OSI architecture was developed as an international standard to define the requirements for security and characterizing the way to satisfy that requirements. You are required to carefully study the OSI security architecture then identify and relate the following scenarios with security services provided by OSI. You are required to provide your answer in table given below:
-
A person, transferring money to his friend using online banking service. Both the bank and the user should be guaranteed in identities of each other.
-
In online banking application a user may be allowed to see his profile, but not allowed to make any changes in his profile information.
-
A user withdraw money from his bank account, but later denied that. How the bank can handle such situation?
-
A user wants to pay his electricity bill using online banking service but website of that bank is down in that time.
-
A user sends a query to bank head office to know about his closing balance and he should receive same balance amount as sent by bank authorities.
Solution:
Best of luck
-
Q. 1 Solution

Scenario. No Associated C.I.A security component 1 Confidentiality 2 Integrity 3 Availability 4 Availability 5 Confidentiality 6 Integrity 7 Integrity 8 Confidentiality 9 Availability 10 Confidentiality Q. 2 Solution

Scenario. No Security Service by OSI 1 Authentication 2 Access control 3 Nonrepudiation 4 Availability 5 Integrity -
-
Q. 1 Solution

Scenario. No Associated C.I.A security component 1 Confidentiality 2 Integrity 3 Availability 4 Availability 5 Confidentiality 6 Integrity 7 Integrity 8 Confidentiality 9 Availability 10 Confidentiality Q. 2 Solution

Scenario. No Security Service by OSI 1 Authentication 2 Access control 3 Nonrepudiation 4 Availability 5 Integrity -
• CIA triad
Question No. 1 [Marks: 10]Suppose you are attempting the exam for the post of Information Security Engineer in the ABC organization. During the exam, you are given the following real life scenarios associated with the three main pillars of informing security (C.I.A) :
- Suppose fifty cancer patient’s treatment is being carried out by Dr. Ali in the well-reputed cancer hospital in Lahore. All the medical information of those patients is stored in the table of the hospital’s database system. Dr. Ali suggests medicine to the patients on the basis of patient’s relevant information stored in the database. If another doctor who has also legal rights to access this table of the database, unintentionally changes the information that can mislead the patient treatment.
- CSS Exam’s applicants are checking their results online through the FPSC website but the FPSC website takes too much time to load.
- The AZB limited Bank makes a plan for launching a new offer for capturing customers in a market but this plan leaked to its competitors.
- A bank’s ATM is not responding due to general backend server error.
- If a renowned shoe brand’s prices and specifications available on online shopping stores are changed by an unauthorized person.
- If you are replying to the messages of your friend, then it should be received in the original form as it is sent by you.
- Upon the last date of applying for the online job application, the related website is not responding due to some technical problems which makes the candidates unable to submit their job application on time.
- Student’s board results information (Marks, CGPA) is considered very important and it should be available only for that specific student and their parents rather than other class students.
- A developer’s salary slip in the software house should not be visible to any other developer.
- Student’s semester grades are posted on the class Facebook group by some unauthorized student.
After carefully reading and analyzing the above-mentioned scenarios and fill the following table:
Scenario. No Associated C.I.A security component
1
2
3
4
5
6
7
8
9
10kindly i want solution of this question plzzz